Summary of knowledge and references related to the terms used and their definitions applied to the topic of integral safety.
2.1.1 assets
An asset is defined as a physical, logical or cyber item that determines the structure and behaviour of the monitored system [6]. The results of the works [1,4] provide lists of identified assets of the model metro station and the Prague metro management system (i.e. people, assets including technology, energy information and material flows), mainly based on the analysis of metro documentation [1,4,10,11]. Since it is an open system of systems, it is necessary to consider other aspects besides the technical part considered in [1,4], i.e., e.g., organizational, financial, functional, logical links, etc. For the purpose of further analysis and we consider the following groups of assets: design, technology, personnel, locations, functions, links and flows, organization and economics.
2.1.2 Disasters
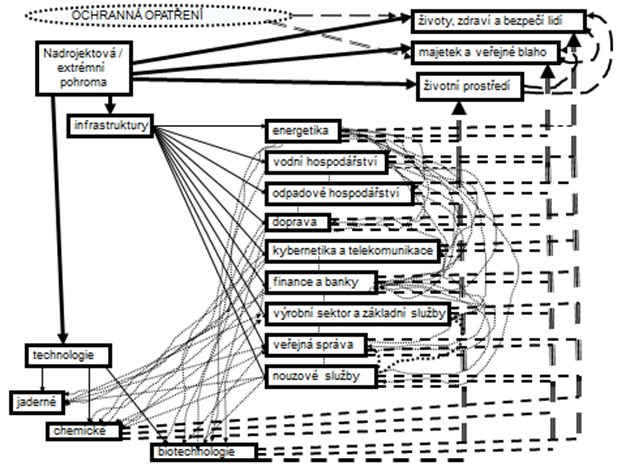
The cause of risks are disasters (of all kinds), the so-called All-Hazard-Approach [12]) and in the case of risks in technological systems, it is also failure states due to random or systematic errors of the system [4,13]. From the above, it can be seen that the occurrence of one extreme disaster can trigger a chain of other disasters, i.e. secondary impacts, and a whole cascade of impacts. Secondary, tertiary and other impacts are referred to as indirect impacts. The indirect impacts of extreme disasters are illustrated in Figure 1. Figure 1 shows the interconnection of the impacts of an extreme disaster with various protected assets that trigger additional impacts on other assets, i.e. indirect impacts that take the form of cascades (i.e. cascade effect).
Based on the magnitude of damage and loss to public assets and the probability of occurrence, i.e. based on risk analysis and evaluation using the risk matrix method of [13], disasters in security management can be categorized into three categories:
Critical disasters: may cause a critical situation in the monitored area or part of it, in which, according to the current Czech legislation, a crisis situation may be declared, and therefore it will be necessary to restore the property after the crisis situation. From a security management perspective, preventive and mitigating measures need to be taken in spatial planning, design, construction and operation of civil and technological facilities and infrastructure.
Specific disasters: they can trigger emergency situations and therefore need to be anticipated in response and preparedness (mitigation measures). From a security management perspective, preventive measures need to be taken in the planning, design, construction and operation of civil and technological facilities and infrastructure, and mitigation measures in response preparedness.
Disasters relevant: all other disasters that may affect the entity and are not critical or specific. They should be handled by normal standard means, i.e. prevention in practice. In terms of security management, existing measures implemented in the spatial planning,
- design, construction and operation of civil and technological facilities and infrastructure are sufficient and therefore only regular monitoring of their effectiveness is necessary.
For the purposes of the present dissertation, the following disasters were used, identified in [4] by analysing archival documents of the capital city. Prague [15]:
Results of processes taking place outside and inside the Earth: flood, windstorm, earthquake, bedrock liquefaction, gas ascent to the Earth’s surface.
Results of processes in the human body, in human behaviour and processes in human society: epidemic, pandemic, disruption of the stability of human society, attack, terrorist attack, attack using chemical, nuclear, radiological and biological (CBRNE) weapons, armed conflict, war.
Results of human-installed processes and activities: industrial accident, hazardous materials transportation or storage accident, transportation accident, critical infrastructure disaster, economic disaster, territorial infrastructure disaster, cyber infrastructure disaster, service, supply and communication infrastructure disaster, technology failure, loss of service.
Interaction of planet Earth and the environment on human activities: disturbance of subsoil stability due to vibrations, air contamination, water contamination, rapid climate variations, migration of large groups of people.
Internal dependencies in the human system by nature or by human creation: organizational accidents, disruption of flows of raw materials and products, disruption in the flow of energy, disruption in the flow of information.
Table 1 provides a breakdown of the disasters that are relevant to the capital city. Prague into categories, details are given in the paper [4]. I.e., it considers the All-Hazard-Approach [12,13] and data [15]; details are in papers [12,13,16].
Table 1 Distribution of disasters – relevant, specific, critical.
| Relevantní | Specifické | Kritické | |
| Výsledky procesů probíhající vně i uvnitř Země | |||
| Povodeň | ano | ano | ano |
| Vichřice | ano | ano | |
| Zemětřesení | ano | ||
| Ztekucení podloží | ano | ano | ano |
| Výstup plynu na zemský povrch | ano | ||
| Výsledky procesů v lidském těle, v chování lidí a procesů v lidské společnosti | |||
| Epidemie | ano | ano | ano |
| Pandemie | ano | ano | ano |
| Porucha stability lidské společnosti | ano | ano | |
| Kriminalita | ano | ano | |
| Útok | ano | ano | |
| Teroristický útok | ano | ano | ano |
| Útok za použití chemických, jaderných, radiologických a biologických (CNRB) zbraní | ano | ano | ano |
| Ozbrojený konflikt | ano | ano | ano |
| Válka | ano | ano | ano |
| Výsledky procesů a činností instalovaných lidmi | |||
| Průmyslová havárie | ano | ||
| Havárie při přepravě či skladování nebezpečných látek | ano | ||
| Havárie při dopravě | ano | ano | ano |
| Pohroma v oblasti kritické infrastruktury | ano | ano | |
| Pohroma v ekonomice | ano | ||
| Pohroma v územní infrastruktuře | ano | ||
| Pohroma v kybernetické infrastruktuře | ano | ano | |
| Pohroma v infrastruktuře služeb, zásobování a spojení | ano | ||
| Selhání technologií | ano | ano | ano |
| Ztráty obslužnosti | ano | ||
| Interakce planety Země a životního prostředí na činnosti lidí | |||
| Porušení stability podloží vlivem vibrací | ano | ano | ano |
| Kontaminaci ovzduší | ano | ano | |
| Kontaminace vody | ano | ano | |
| Rychlé variace klimatu | ano | ||
| Migrace velkých skupin lidí | ano | ||
| Vnitřní závislosti v lidském systému přirozené nebo lidmi vytvořené | |||
| Organizační havárie | ano | ano | ano |
| Selhání toků surovin a výrobků | ano | ||
| Selhání toků energií | ano | ano | ano |
| Selhání toků informací | ano | ano | ano |
2.1.3 Risk and Criticality
The concept of risk has different and inconsistent conceptualizations in many areas, with some definitions of risk based on probability and others based on expected value or uncertainty and indeterminacy [17]. From a project management and management system perspective, risk has generally been defined as “the effect of uncertainty” [18]. The effect of uncertainty, when realized, can take on negative as well as positive characteristics (i.e., opportunities) [18].
Risk in engineering disciplines such as system risk management, reliability management, and safety risk management expresses the likely magnitude of unacceptable (i.e., unwanted) impacts (losses, damages, and harm) of a hazard magnitude disaster (i.e., disaster potential normatively determined) on protected interests (assets) over a specified time interval at a specified location [17].
The source of these risks are the disasters mentioned in the previous paragraph. These are risks to people, their property, the environment, critical infrastructure and, last but not least, the state. The risks can be categorised according to the protected assets selected for risk consideration and whether a single protected asset (i.e. partial risk) or a set of protected assets (integrated risk) or a set of protected assets and the links and flows between them (complex risk/integral risk) are being monitored.
Furthermore, risks are divided according to which disasters or disaster sources are considered (only some disasters, part of their scenarios or all relevant disasters, etc.).
In common practice, and especially for transport systems, partial and integrated risks are usually considered, which are usually expressed as the product of the probability of occurrence of a disaster (or incident or failure) or the frequency of occurrence and the magnitude of their impact (losses, damages, harm) on the entity or selected set of entities under consideration. There may be many variables for calculating the risk depending on the area being monitored, but usually it is the product of the above two. In more detailed studies, the degree of vulnerability and sometimes also the degree of controllability of the harmful event is considered; for example, in the automotive industry [19].
Thus, we observe many differences in the understanding of risk (R) and the only commonality is that risk is based on the fear of an uncertain future [5,17]:
R = frequency ∙ consequences;
R = severity ∙ possibility of occurrence;
R = threat ∙ vulnerability;
R = threat ∙ vulnerability ∙ impacts;
R = threat (threat) ∙ vulnerability / capacity;
R = (threat (threat) ∙ vulnerability) / countermeasures ∙ impacts;
R = f (threat (threat) ∙ vulnerability / capacity);
R = f (asset (protected interest) ∙ threat (threat) ∙ vulnerability);
R = frequency ∙ population ∙ vulnerability.
In order to ensure a safe area, or larger technological units or facilities, it is necessary to take into account complex risk, i.e. integral risk based on a systemic concept of reality [2]. Integral risk includes multiple protected assets including life, health and safety of people, property and public welfare, the environment as well as technology and infrastructure, and includes the impact of interdependencies between these protected assets [4,17].
The integral risk, denoted as R, for all disasters in an area is given by the relationship [17]:
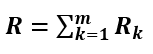
(1)
Rk expresses the risk for the kth disaster:
(2)
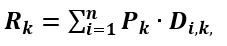
Pk denotes the probability of occurrence of the kth disaster and Di,k the impact of the kth disaster on the i-th protected interest. Similar relationships are applied for integrated risk, but with the difference that the Di,k impacts for integral risk include not only direct DDi,k impacts but also indirect (secondary, tertiary and more) DIi,k impacts, whose relationships are as follows according to [19]:
(3)
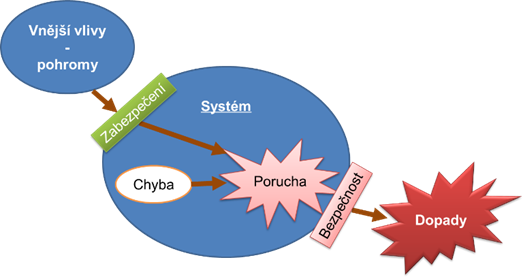
Vi is the value of the protected interest, S is the monitored area or object, Zi,k is the vulnerability of the i-th protected interest in the event of the k-th disaster, Ii,k is the interdependence function. The interdependencies depend on the specific structure of protected interests in the territory and the specific interconnections of protected interests and on the disaster, i.e., according to [17]:
(4)
VDk is a characteristic of the rate of the kth disaster that affects impacts on protected assets. VPi,k is a characteristic of the degree of interconnectivity of protected interests in a given area. The determination of VPi,k is the subject of detailed research based on Boolean logic or, for more complex linkages, on operational analysis methods [17,19,20].
For technical systems [21], the relation holds:
(5)
in which H is the hazard associated with a given disaster at the site; Ai are the values of the monitored assets for i = 1,2,…, n; Zi are the vulnerabilities of the assets for i = 1,2,…, n; F is the loss function; Pi are the probabilities of occurrence of damage to the assets for i = 1,2,… , n – these are conditional probabilities; O is the vulnerability of protective measures; S is the size of the monitored asset; t is the time measured since the occurrence of the damaging event; T is the time over which losses occur; and t is the disaster recurrence period. Since the loss function is usually unknown, failure scenarios are created and multicriteria methods are used to estimate the risk; usually decision support systems [22].
From the above knowledge and due to the complexity (intricacy) of the systems, it is clear that integral safety can only be improved by considering and managing integral risks that do not only consider the sum of the partial risks, but also account for the links and flows between assets [13].
For the purpose of security management, the criticality of an asset (K) is a function of the importance and vulnerability of the asset under consideration or even of the whole entity expressed as a product [13,17]:
K = importance ∙ vulnerability (6)
Criticality with respect to a certain disaster can be expressed by the relationship
C = S ∙ O ∙ B (7)
in which S is the severity of the greatest impact of the disaster (harmful event), O is the probability of the disaster occurring, and B is the conditional probability that the most severe impact will occur [13,23].
Risk, as mentioned in the introduction of this paragraph, refers to the effect of uncertainty, i.e., how often (or how likely) losses will occur. By reducing risk, we reduce the frequency of occurrence of an adverse event (as far as it is within our control) or its impact. In this way, risk is related to safety, but it is not defined by safety. Criticality refers to the limit (threshold) value between two states, in the safety domain it is the undesirable (hazard) and the desirable (safety). By reducing criticality, i.e. the threshold value between hazard and safety, we increase the state space of the system in the safe domain, i.e. we increase safety. Therefore, criticality is a complementary quantity to safety, even though criticality is a consequence of risk factors and may have the same input parameters (e.g., vulnerability) with risk [27].
2.1.4 Safety
In current practice, several different meanings are attached to the term security. In transport systems, the term safety is associated with: the protection of people without considering the links to the system; the resilience of the system against disruption by an adverse event (disaster); or against internal faults. In conjunction with protection or safety systems, safety is understood as so-called functional safety, i.e. the realization of a safe function or process in case of foreseen situations [24]. In fact, the aforementioned meanings have the same goal, to protect people’s health and lives, and to ensure the development of human society, i.e. all meanings are part of an integral safety that brings them all together.
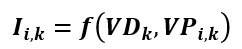
System security in the context of integral security means that the system is protected against internal and external disasters, including the human factor, i.e. the system has sufficient resilience and adaptability to expected conditions. Moreover, a secure system must not fail to endanger its environment even in its critical conditions [20,25,26,27], Figure 2 according to [20].
The potential effects of the system failures shown in Figure 2 will manifest themselves in other systems as a disaster in their environment, in which case a confluence of disasters, i.e., a cascade effect, is created.
According to current knowledge, the term Safety means a set of means and measures by which humanity ensures its security and sustainable development. Figure 3 illustrates the concept focused on safety, i.e. a higher goal; it is not just about reducing risk, but about increasing the safety of people and other public assets on which people depend [27].

The above shows that safety and risk are related, but they are not complementary variables, because safety can be increased by organisational measures that do not affect the size of the risk. Criticality is a complementary variable to safety. By reducing criticality, we increase the safety of the monitored object.
2.1.5 Human security and integral safety
Human security, which is the goal of security management, is a topic that has been known since the beginning of mankind, but it is only recently defined in the field of security sciences. The United Nations has defined Human Security as a concept that means:
“… to protect the essential foundation of all human lives in a way that enriches people’s freedom and self-realization. Human security means protecting the foundations of freedoms – the freedoms that are the essence of life. It means protecting people from critical (severe) and pervasive (widespread) threats and situations, It means using processes that build on people’s strengths and aspirations. It means creating political, social, environmental, economic, military, and cultural systems that collectively provide the building blocks for people to survive, earn a living, and enjoy dignity… ” [8].
It is therefore primarily a change in approach from simply protecting the state from threats from hostile armed forces to one that emphasises people’s lives and protecting them from other known threats. According to the UN, the core areas of the concept of “Human Security and Threats” are as follows [8]:
economic security (persistent poverty, unemployment),
food security (hunger, famine),
health security (deadly infectious diseases, unsafe food, malnutrition, malpractice in basic health care),
environmental security (environmental degradation, resource depletion, natural disasters, pollution),
personal security (physical violence, crime, terrorism, domestic violence, child abuse),
political security (inter-ethnicity, religion and other identity-based tensions),
political security (political repression, human rights abuses).
In terms of economic security, the concept of Human Security emphasises the rehabilitation of transport and transport routes. Transport is a condition for the successful fulfilment of the objectives of the individual security areas, i.e. the concept of Human Security, but at the same time it can damage the subject of the individual objectives by its own errors and weaknesses. Consequently, transport and the transport system create new threats, which are, for example, pollution, direct impact on people’s lives and health and property [19].
States ensure the security of people and individual security objectives through the so-called core functions of the state. One of the means is infrastructure [2]. The focus of the present work is transportation infrastructure and related critical infrastructure (e.g., critical information infrastructure).
The tool to ensure the security of people is integral security, which is provided by different types of security methods and technologies. It covers other engineering areas such as reliability management, functional security, cyber-physical systems security, technical and physical security, security, workplace security, people security, etc. Integral security deals with the security of multiple assets in the study area that interact with each other, are interdependent and have different types of links with higher-level and surrounding systems. The concept of integral security also considers the occurrence of all possible sources of threats that may affect the entity under study [2]. Integral security management works with integral risk management [19].
The real world we perceive is not ideal, and therefore conflicts arise because of imperfections and differences in it. Conflicts also arise in the different areas of security, safety and interdisciplinary contexts. The consequence is that by increasing the security of one element of the system under study, we may inversely degrade the security of another element, thereby affecting integral security and the overall safety of people.
From the above, it can be seen that in order to ensure integral safety, it is not enough to increase the safety or security of the individual elements of the system, which through their interconnections form a complex system, but we must ensure a more effective management system that is able to deal with the complexity of the real world in the best possible way [19].
The improvement of integral safety is based on process and project management, which aim to continuously improve the quality and maintain a certain level of safety of systems under dynamically changing real-world conditions (surrounding physical conditions, links with other systems, changes in culture and behaviour of individuals or groups of people, etc.). In European Union conditions, project management of the type called Total Quality Management (TQM) is used [28]. For its success ISO standards of 9000, 14000 class etc. have been created.
The TQM approach is based on the requirement that all employees, from the rank and file to the top management of the entity, participate in the quality improvement process of the entity. The process of quality improvement (i.e. at its highest level it is de facto an improvement of integral safety) is based on impulses that come from the needs of the customer or citizen [29,30]. TQM is based on the assumption that the sustained quality (quality) of products and services cannot be ensured by orders, controls, partial programs, organizational or economic measures, but by purposeful search, measurement and evaluation of the causes of why productivity and quality are not increased; de facto it is a certain culture of safety (in other words, the way measures and people’s actions are applied). The focus is on the processes taking place in the entity. The implementation of TQM takes into account the specifics of the entity because, for the sake of effectiveness, all measures have to fit the structure of the entity, i.e. they have to be site specific [19,30].
In addition to the standardised management systems (ISO standards), which are based on TQM principles, TQM also includes principles and attitudes for the management of soft socio-technical systems, with simple idealised objectives so that they are understood by all the personnel concerned or the inhabitants in the place under consideration. In terms of safety, TQM builds so-called Total Safety Systems (TSS for short). TSS introduces the concept of Zero Risks, which is the basis for following a Zero Defects strategy and doing things right the first time.
Incorporating specific prevention into the safety of socio-technical elements of organisational systems involves comparing the contributions of the so-called Total Prevention Systems (TPS), which incorporate Zero Breakdown principles, and the Human Development System (HDS), which is designed to educate and train workers on the principle ‘right first time’ [28]. These total prevention systems include, for example, the implementation of the well-known Total Operation Maintenance [28], etc.
The overall (integral) safety system includes three basic elements:
site safety (layout, environmental management, emergency procedures, fire precautions, first aid, lighting, social facilities, etc.),
process safety (physical security, emergency stop elements, fail safe principles, perimeter protection),
human resource safety (safety training, personal protective equipment, supervision, health checks).
The EU has issued a checklist, largely used for inspections, covering the three areas mentioned above [2]. The TQM system together with the TSS in many areas significantly exceeds the legislative requirements in force in the Czech Republic. For the purpose of improving safety, the basic premise of the introduced systems is the reduction of risk, by means of proactive programmes with continuous measurement and elimination of near-misses. Near-misses are events which, based on current knowledge, would normally lead to an accident or crash, but in a given case no problem occurred, e.g. due to the presence of mind of the operator [19,21,28].
Current trends in security science and risk engineering are based on the principles of engineering risk management, considering the complexity of systems that arises from the nature, properties and uncertainties of socio-technical, cyber-physical systems, referred to as systems of systems (abbreviated as SoS) [2,19,26,30,31].
2.1.6 Critical infrastructure and its security
Critical infrastructure is defined in terms of Council Directive 2008/114/EC on the identification and designation of European Critical Infrastructures and the assessment of the need to improve their protection [32] as: ‘Assets, systems and parts thereof located in a Member State which are essential for the maintenance of essential societal functions, the health, safety, security or the economic or social well-being of the population and the disruption or destruction of which would have a serious impact on a Member State as a result of the failure of these functions’. According to the source [33], in other words, critical infrastructure can be defined as systems of different nature (technical, organizational, cyber, territorial, educational, etc.) that can affect the functioning of the economy, the state and the management of emergency and critical situations. In the Czech Republic, critical infrastructure consists of infrastructures divided into the following nine areas [33]:
Energy supply (electricity, gas, heat, oil and petroleum products).
Water (provision of drinking and drinking water, provision and management of surface and groundwater resources, wastewater system).
Food supply and agriculture (food production, food care, agricultural production).
Health care (pre-hospital emergency care, hospital care, public health protection, production, storage and distribution of pharmaceutical products and medical equipment).
Transport (road, rail, air and water).
Cyber, communications and information systems (fixed and mobile telecommunications network services, radio communications and navigation, television and satellite communications, mail and parcel services, internet and data services).
Banking and financial sector (public financial management, banking, insurance, capital market).
Rescue system (Czech Fire Brigade, fire protection units, Czech Police, Czech Army, radiation monitoring, forecasts, warning system, etc.).
Public administration (state administration and local government, social security and employment, state social support and social assistance, administration of the judicial and prison system).
The area of critical infrastructure is regulated by the Crisis Act [34]. An object or element of critical infrastructure is defined as a building, facility, resource or public infrastructure determined according to cross-cutting and sectoral criteria, i.e. according to [35]. From the point of view of the railway system, critical infrastructure objects are, for example, railway stations, metro stations, major bridges or tunnels, technological equipment and information, material, energy flows in systems, according to the methodology for determining the criticality of objects by source [33].
The protection of people’s health and property is the primary interest of the basic function of the state, enshrined in the Constitution of the Czech Republic (Act No. 1/1993 Coll.). Potential disasters may not only affect the proper functioning of a critical infrastructure element, but may also endanger the health and property of people and the environment. Therefore, according to the category of disaster mentioned in the previous paragraph, appropriate measures are implemented [4,13,33].
2.1.7 Modern approaches: All-Hazard-Approach a Defence in Depth
The All-Hazard-Approach [12] means to consider all possible types of disasters, i.e. phenomena that can cause damage, loss and harm to the assets under consideration, i.e. people and relevant entities in a given area [2], when managing safety.
Defence-In-Depth is a comprehensive philosophy of security assurance that began to be applied in technology in the 1980s [27]. In general terms, this approach can be understood as protecting a system using measures at multiple layers of the system.
Based on [36], Defence-In-Depth is a comprehensive approach that ensures that people and the environment are protected even under critical conditions in a facility. It includes all activities aimed at the security of the facility and the area in which the facility is located, starting from siting, through design and planning, construction, construction, commissioning, operation and decommissioning. Barrier systems and regime measures are used to ensure a safe system of systems.
The Defence-In-Depth approach is also known in cyber and control system security, e.g., according to [37], Figure 4.
Figure 4 illustrates the Defence-In-Depth approach as a strategy for security management involving the following areas:
security guidelines,
specification of security requirements,
security by design,
secure implementation,
security verification and validation,
Defence-In-Depth strategy.
The generalised layered model for security management according to the Defence-In-Depth approach used in the thesis is described further in Section 2.3.4.
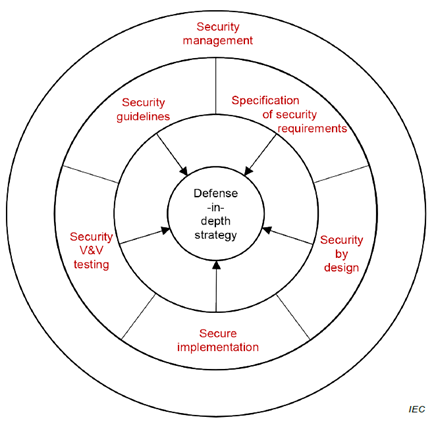
Obrázek 4. Strategie Defence-In-Depth dle [37].
2.1.8 Systems of Systems (SoS), project and superproject phenomena
A system of systems (SoS) is defined in the field of systems engineering [38] as a set of independent systems integrated into a larger system that provides unique characteristics. Independent so-called constituent systems cooperate to produce global behaviors that they cannot produce on their own. In line with [39], the classical notion of system and SoS differ mainly in the following elements:
Autonomy – autonomy is exercised by component systems to fulfill the purpose of the global system, i.e., the SoS,
affiliation – individual component systems choose affiliation according to the cost-benefit ratio, for the sake of fulfilling their own purpose and in the belief in the supra-purpose of the SoS; in the classical concept of the system, affiliation is given according to their nature and cannot be changed arbitrarily (e.g. as a member of one family),
connectivity – the myriad possible interconnections between systems and their parts to improve the capabilities of the SoS,
diversity – higher diversity (variety) in SoS capabilities achieved through autonomy of different component systems, biased affiliation and open connectivity,
emergence – in the SoS concept, increased deliberate unpredictability of the system and the creation of conditions for the possibility of emergence (i.e. emergence) is of fundamental importance in both negative (emergence of unpredictable negative events, disasters) and positive (early detection and elimination of adverse system behaviour) senses.
The emergence element has a major influence on the choice of methods for working with systems, the prevalence of exact methods for classical systems, and the prevalence of heuristic methods for SoS, i.e. including the use of Artificial Intelligence (AI), etc.
For the purpose of this dissertation, we understand SoS as a set of open interconnected systems [33], further composed of subsystems and objects (components) of different properties and their locations. The links between subsystems and objects provide the necessary functionality and behavior of the entire SoS [40]. Interconnections and dependencies, i.e. interdependencies, are physical, cyber, local and logical according to their nature [6]. Furthermore, SoS interdependencies can be divided into:
- Desirable: improve the performance of systems, equipment and infrastructures,
- unwanted:
a) under normal and abnormal conditions: they are treated by the project according to the requirements of the legislation [41],
b) under critical (supra-project) conditions:
leading to system losses,
causing systems to fail to perform their functions properly,
cause systems to endanger themselves and their environment.
Given certain conditions of the system being solved, some situations can be solved by exact methods. These conditions for ensuring safety are set in the design according to its lifetime and criticality, in this case we are talking about design criteria. In the event that adverse events or accidents occur after which the design criteria or conditions are not exceeded, these are so-called design events (accidents). Safety primarily affects the area outside the stated limits and conditions of the systems, i.e. over-design phenomena or accidents.
For example, the terms Design Basis Accident and Beyond Design Basis Accident are formally defined by the International Atomic Energy Agency (IAEA) [42], but are commonly used in other areas of engineering safety management [41].
